Security
10 Best Tips To Add More Value To Your e-Commerce Store
As all of us already know that how important is ecommerce to your business so here in this post we are not going to…
Archive
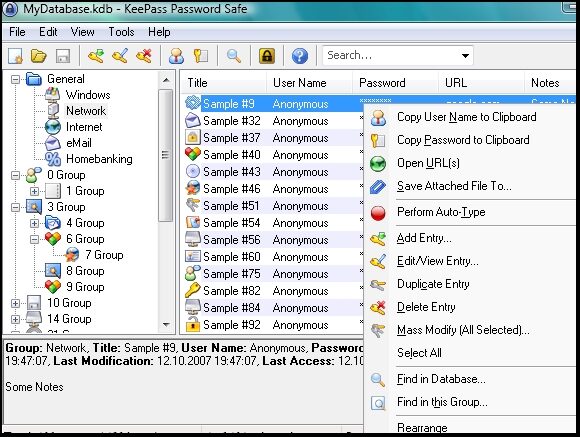
Threats, hardening, privacy, and the operational side of securing software and infrastructure.
Security
As all of us already know that how important is ecommerce to your business so here in this post we are not going to…
Security
There’s no question that cloud computing has major benefits for enterprises of all sizes. Storing data on virtual servers ensures flexibility in access, plenty…
Security
Unfortunately, hacking is at an all-time high and it only seems to be getting worse. This is why you have to be sure to…
Security
As technology continues to transform all aspects of our lives, a lot more people are moving towards careers that involve programming, computer science, and…
Security
In today’s globalized world, it is very hard to imagine our lives without Internet and tons of facilities provided by it. Today, majority of…
Security
There are several essential best practices for secure web application development. Today’s web applications are a core component of modern business operations, digital entertainment,…
Security
Many web servers use a configuration file called .htaccess that is based on the directory level. This file is used to provide decentralized management…
Security
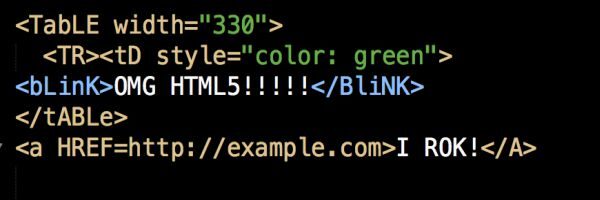
HTML5 is enhancing the platform of the World Wide Web by making it strong in a wide range of areas.HTML5 is regarded as the…

Security
User bulletin boards, forums and chat rooms existed long before Facebook was invented, but Facebook was the first social networking platform to enable legitimate…
Security
More and more webmasters nowadays do not value the importance of a complete website backup (files and databases). They have left this to chance…